Back to: Technology Guides
How to install Active Directory on Windows Server 2019
What is Active Directory?
Active Directory Domain Services is a complete hierarchical authentication system, domain management system and object storage system developed and maintained by Microsoft for the Windows ecosystem.
It used to be a walled garden but you can integrate Linux systems into it these days.
The way that the system is centralized allows an employee with a single user account to log in with same account on all devices that are part of the same company.
Getting started
In order for Active Directory to work, all computers must connect to the main central server called the Primary Domain Controller with Active Directory installed.
In this guide, we are going to assume you already have the following:
Microsoft Windows Server 2019 installed on a server.
You want to connect a client with Microsoft Windows 10 to this server.
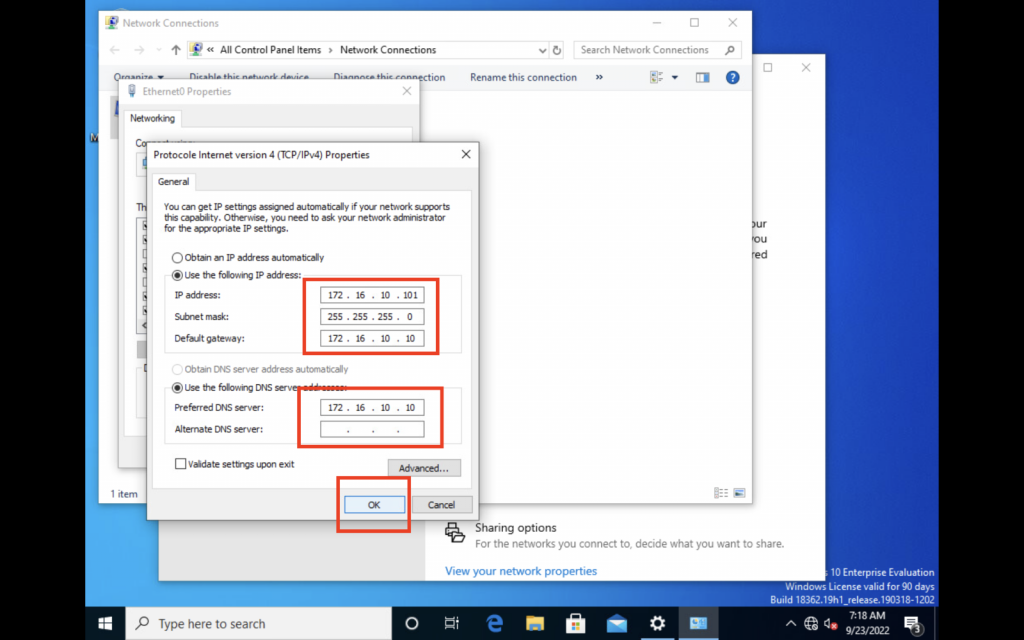
We are going to be using the following network configuration:
Asset | NETBIOS Name | IP Address | Subnet Mask |
Primary DC Server | server-eu | 172.16.10.10 | 255.255.255.0 |
Client Machine | wks-1 | 172.16.10.101 | 255.255.255.0 |
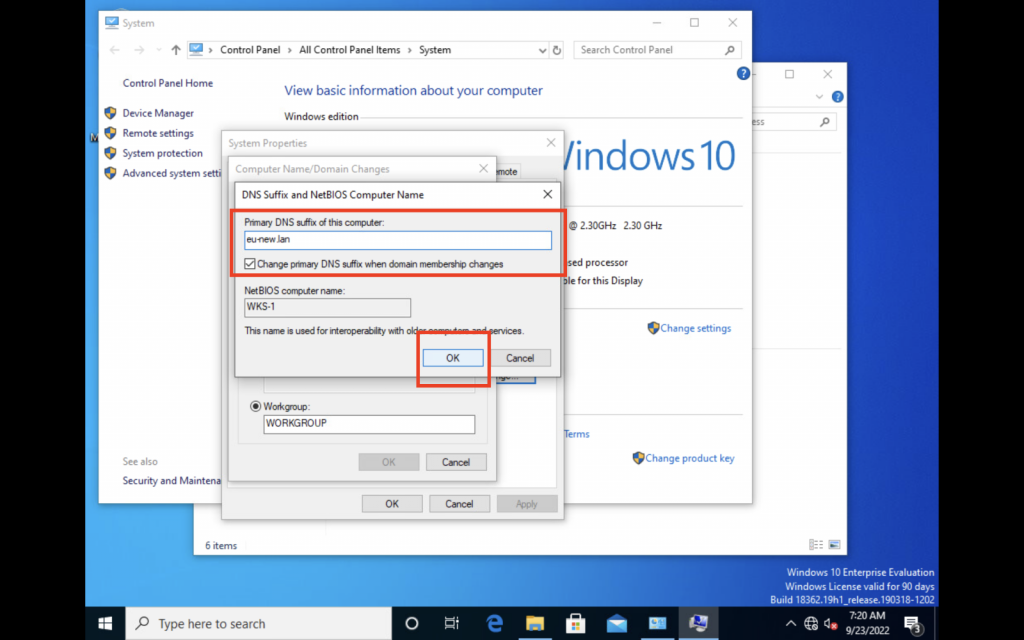
We are going to be using the domain eu-new.lan.
The complete name or Fully Qualified Domain Name (FQDN) of each asset will be:
Primary DC will be:
server-eu.eu-new.lan
Client will be:
wks-1.eu-new.lan
Primary DC configuration
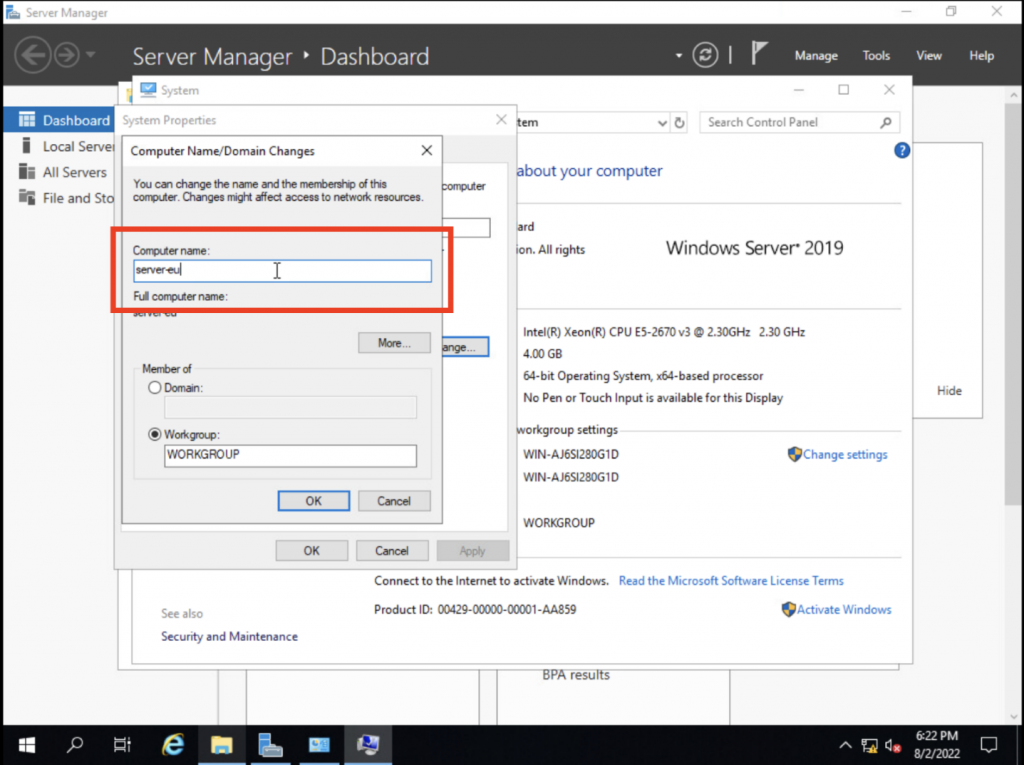
1. Configure NETBIOS name to server-eu
We start by establishing our server's name to be server-eu.
2. Configure network to use 172.16.10.10
We will now configure our server's network to be a static IP address of 172.16.10.10 so that our client will know which address to connect to.
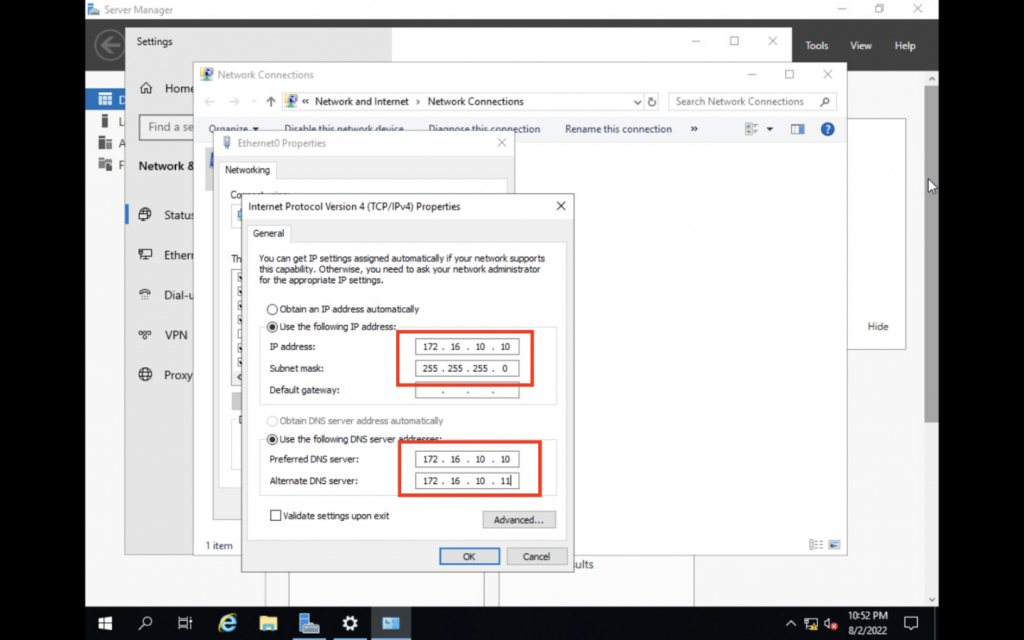
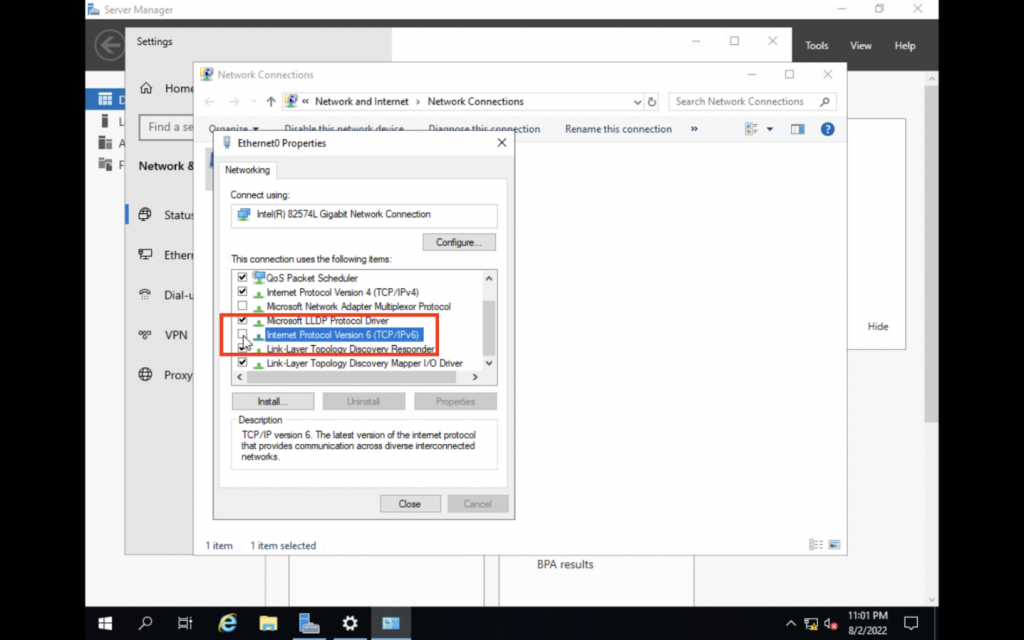
We are disabling IPv6 because we will only be using IPv4 and we want to make sure it will not interfere with our setup.
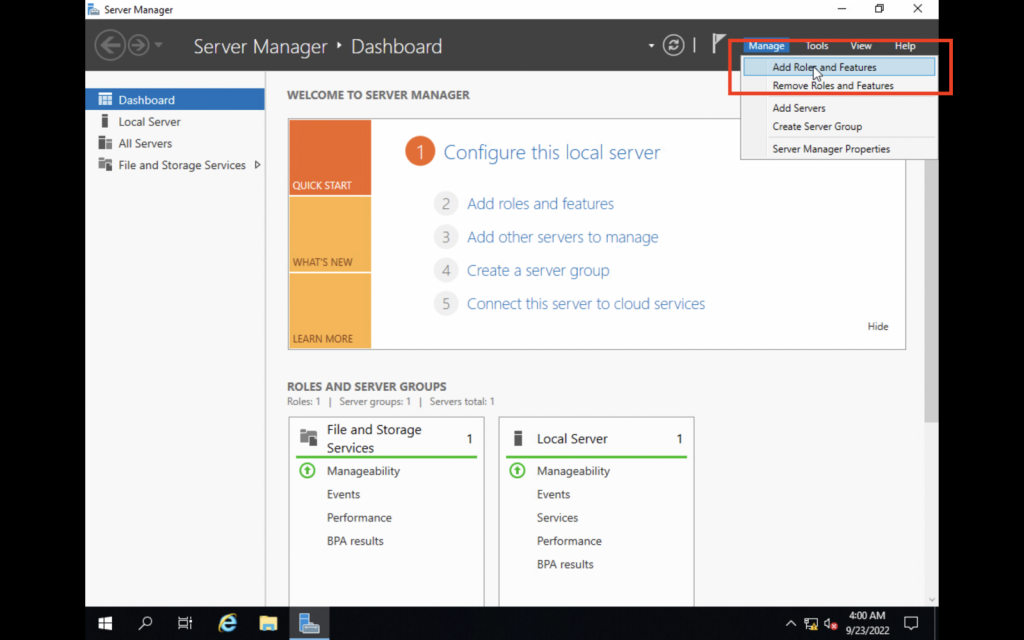
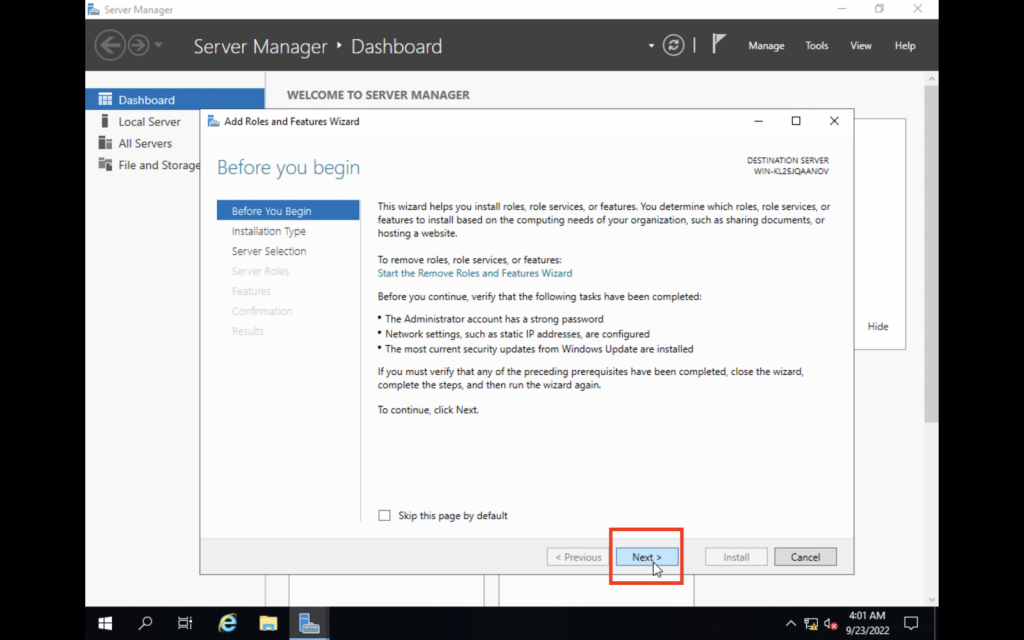
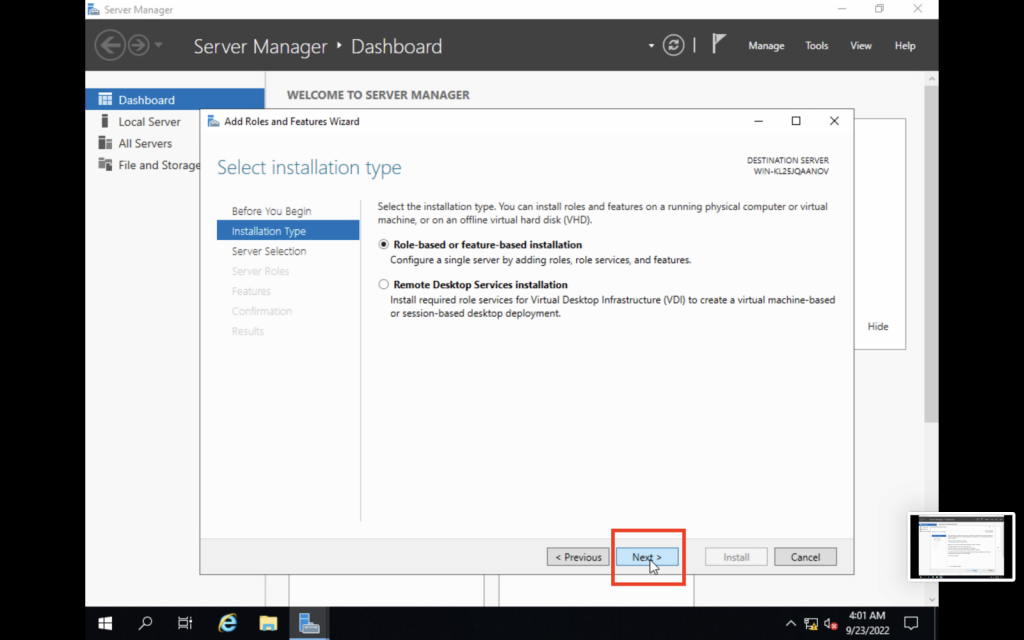
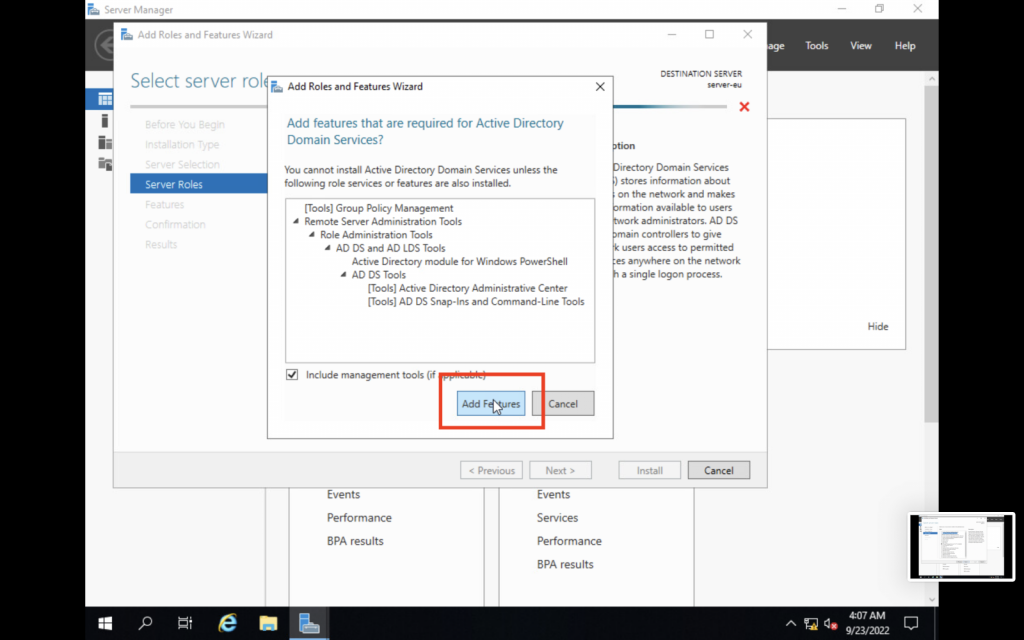
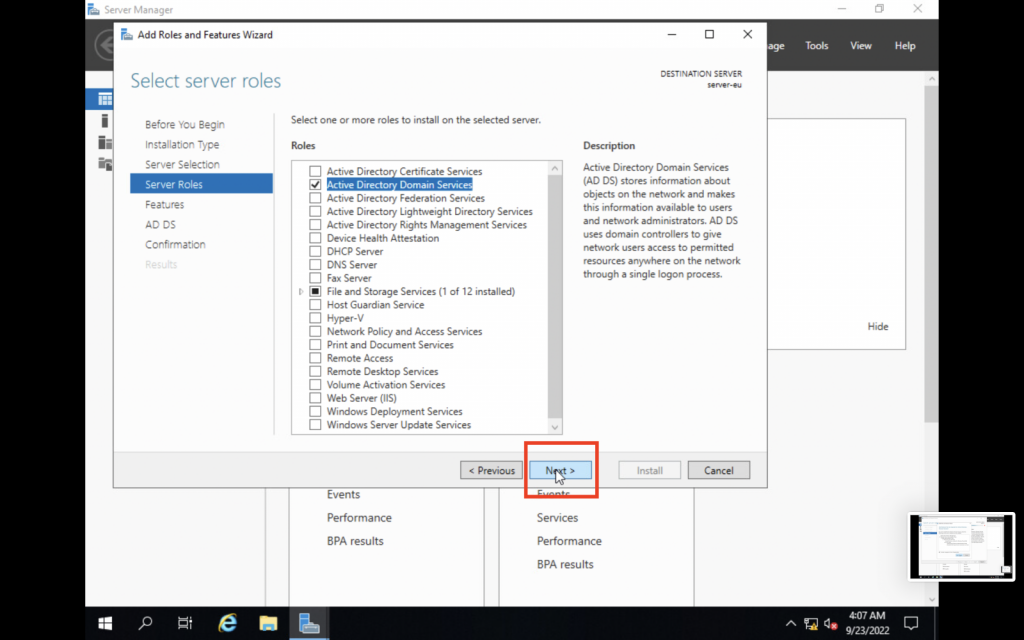
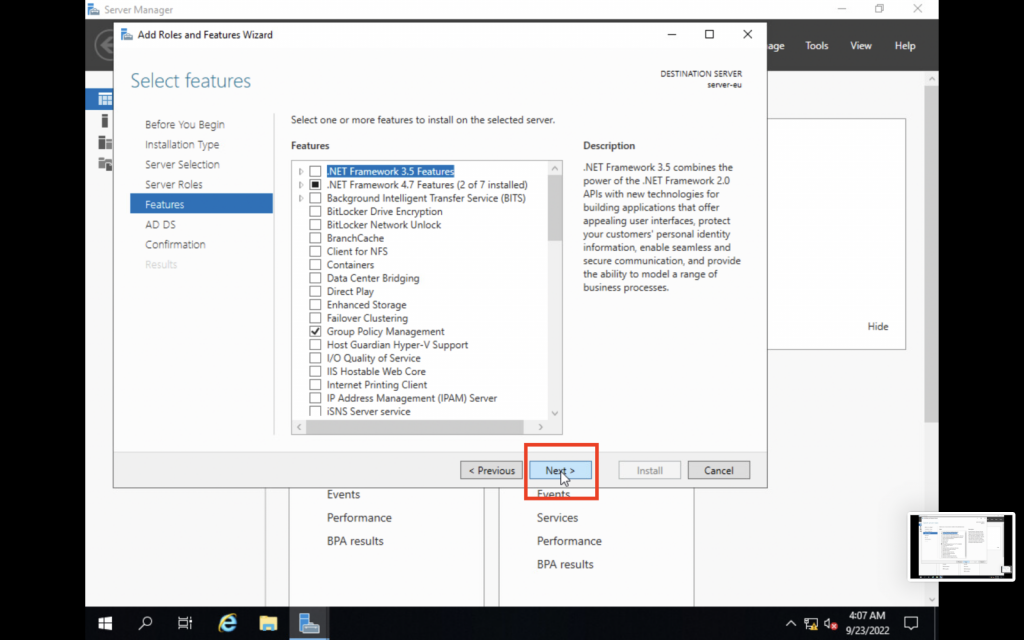
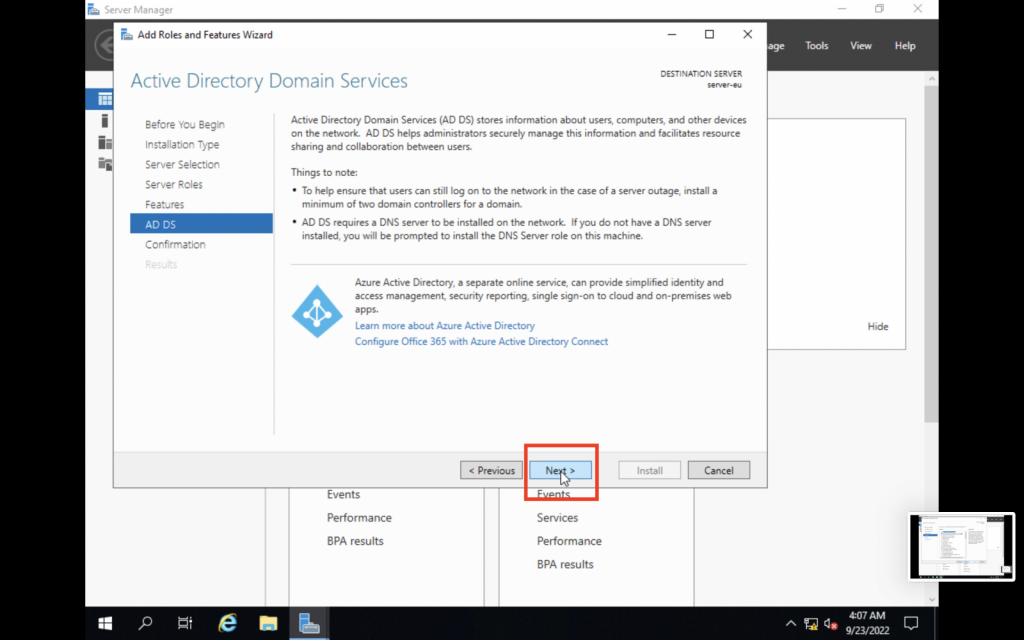
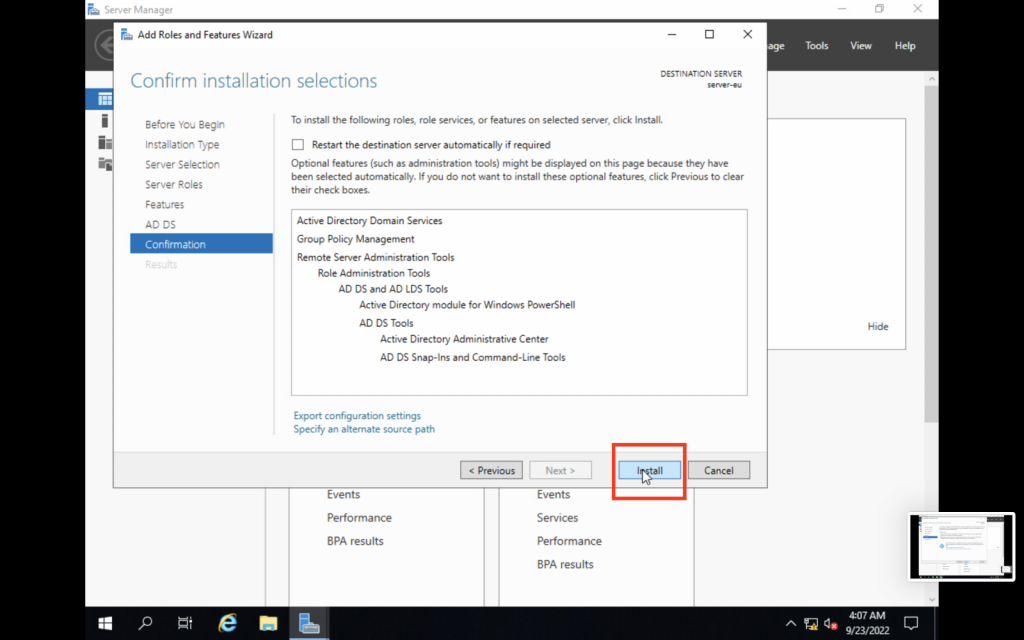
3. Install Active Directory.
Now that our network and computer configurations are in place, we can start installing the Active Directory Domain Services features on our server.
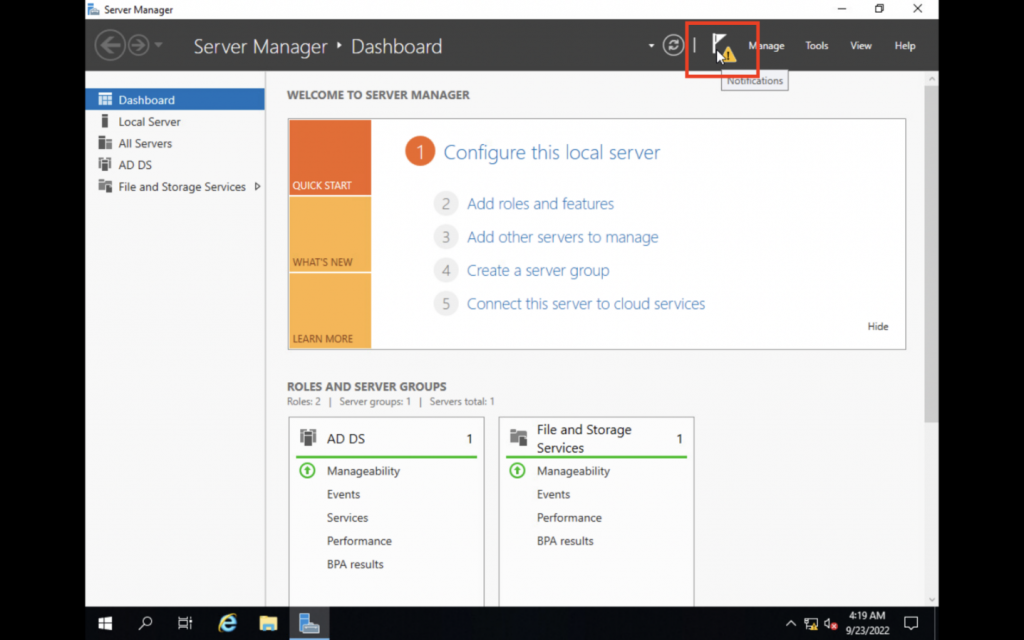
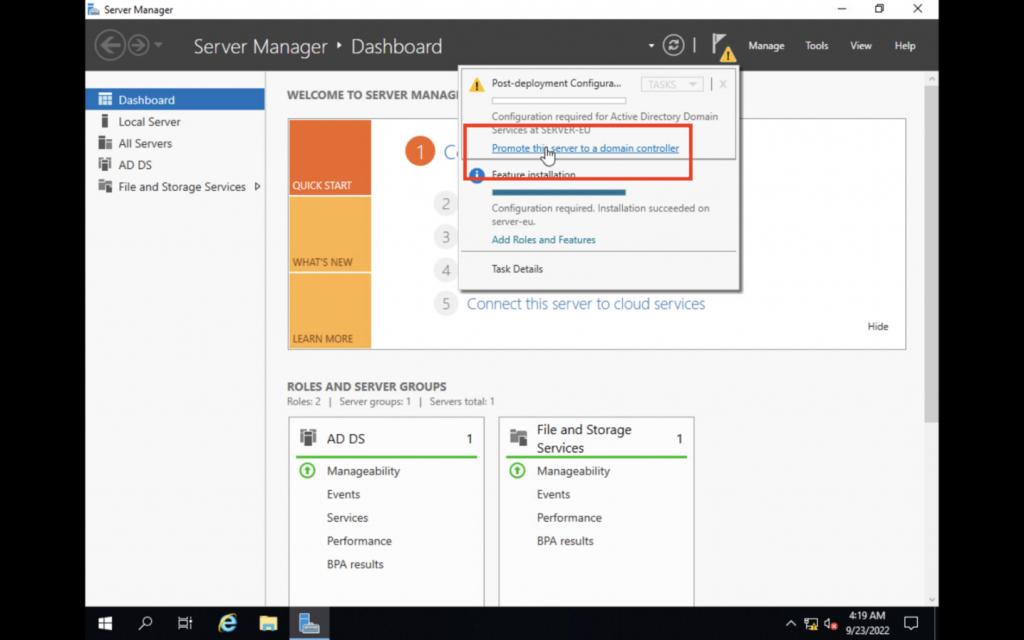
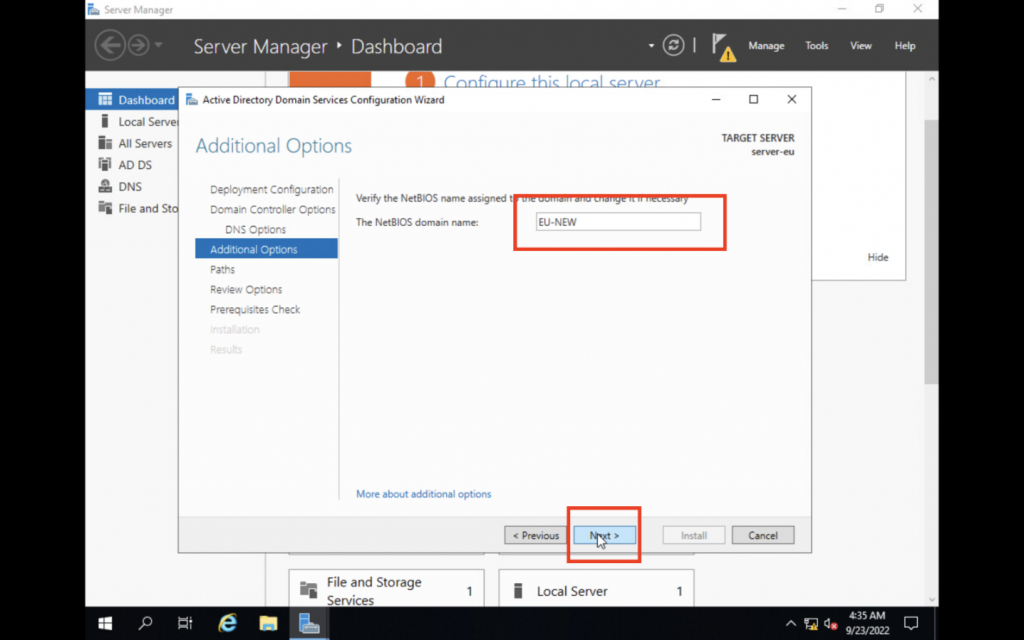
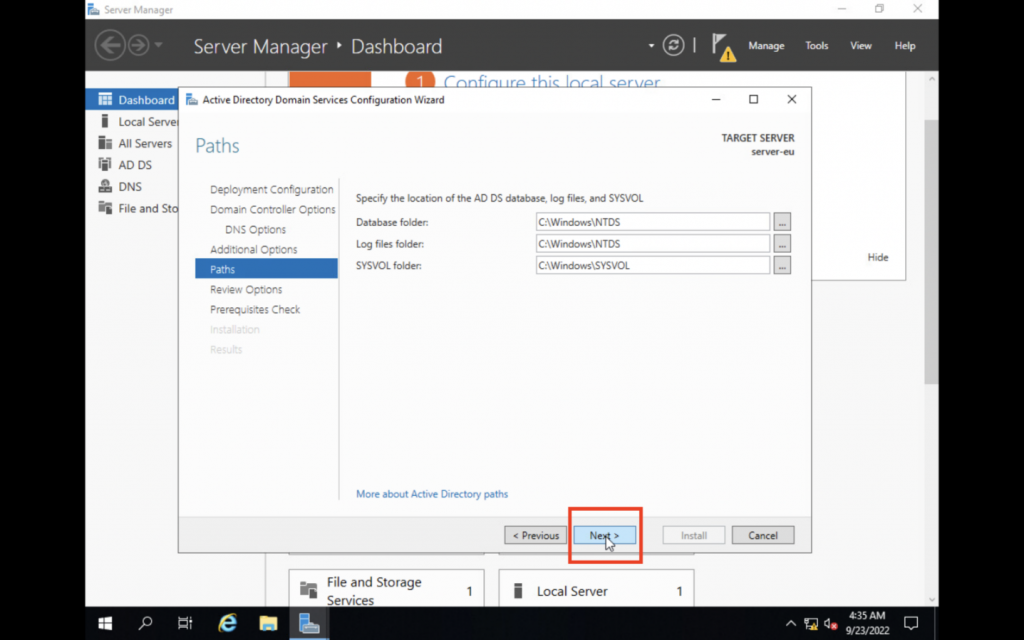
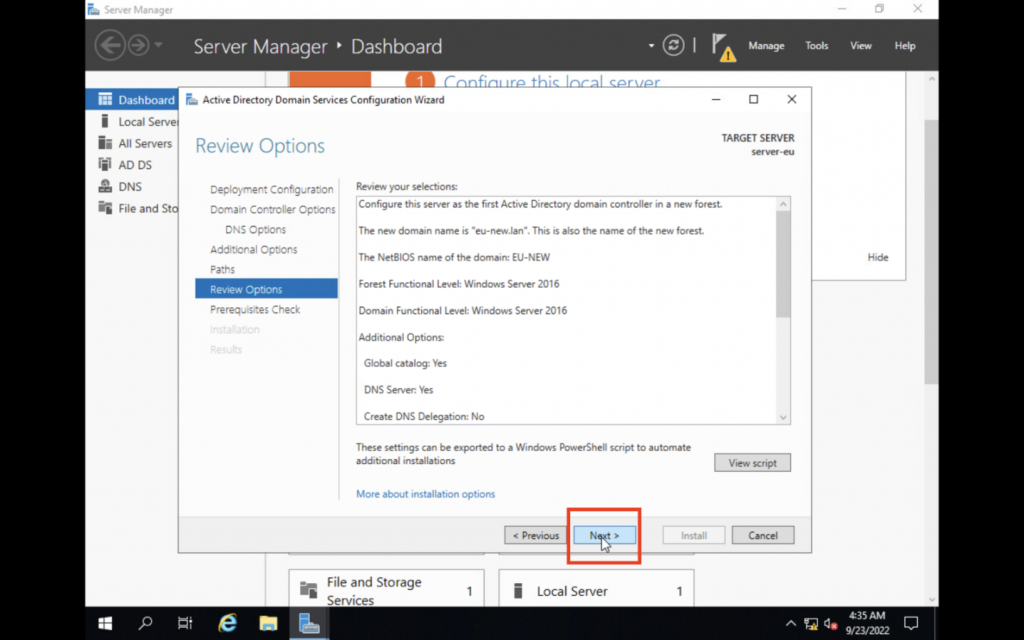
4. Promote the server to become the Domain Controller
After installing Active Directory, we must now promote the server to become the Primary Domain Controller of the domain. The server will become the central authority for all clients to authenticate with.
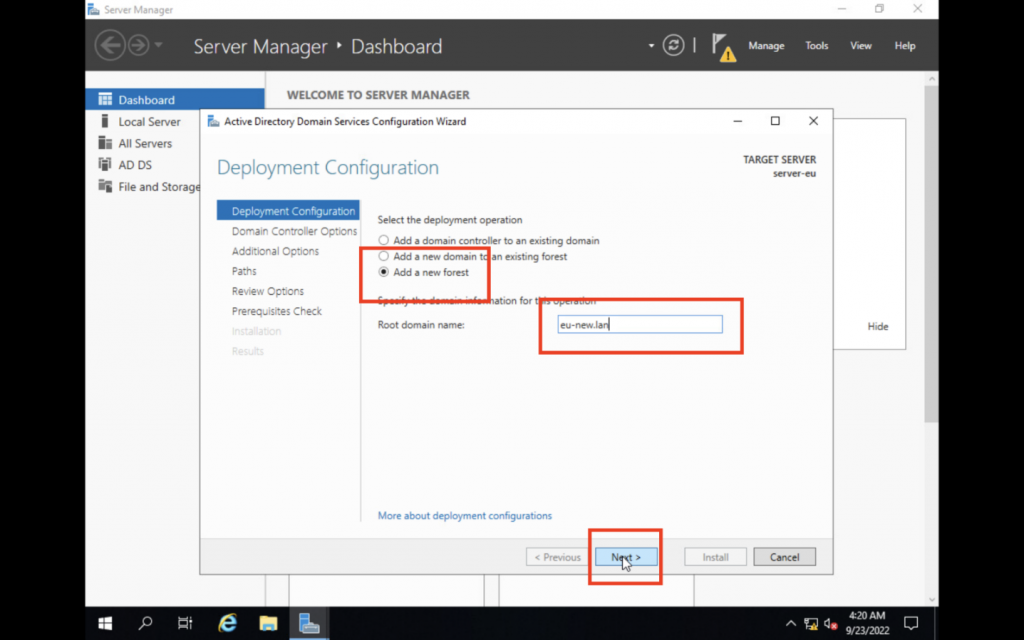
We are choosing to add a new forest because we are promoting our first Domain Controller. In order for that to work, must establish our forest and then create our root domain inside it. We are using eu-new.lan as the root domain.
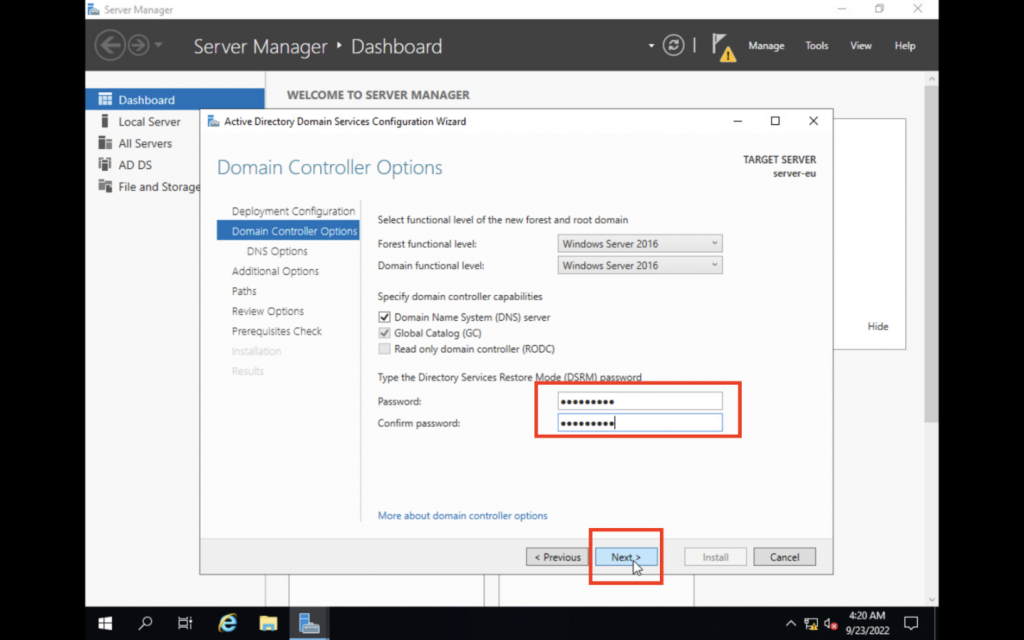
This password needs to be different from all other passwords and must be kept in a secure place. The DSRM password is used to boot a Domain Controller in a restore safe mode if something goes wrong.
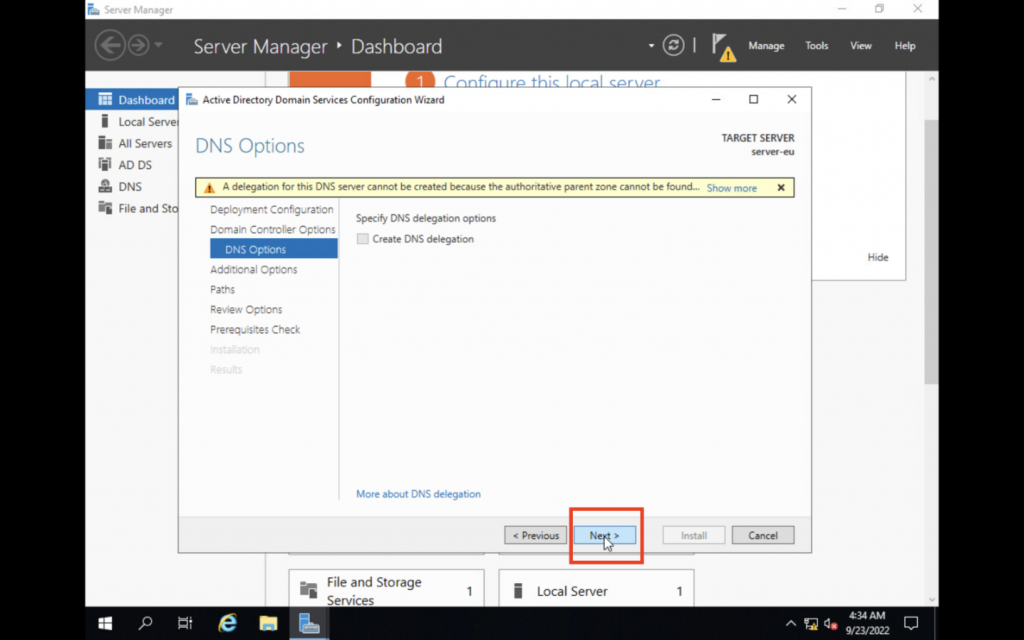
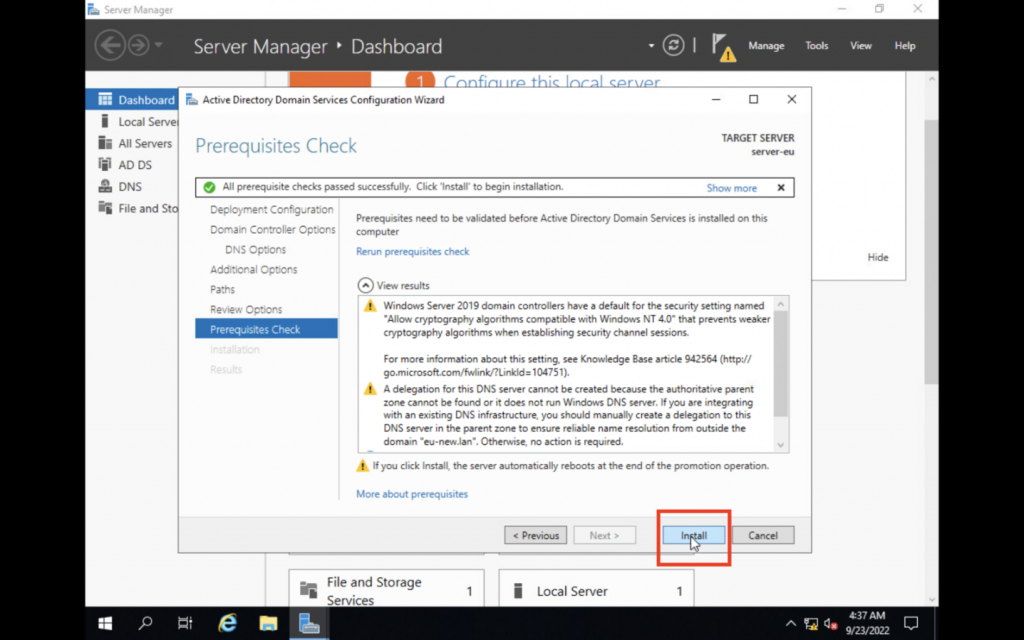
The server has now been promoted to become the Primary Domain Controller with Active Directory installed. All clients of the domain eu-new.lan will now connect to this server in order to authenticate and log in.
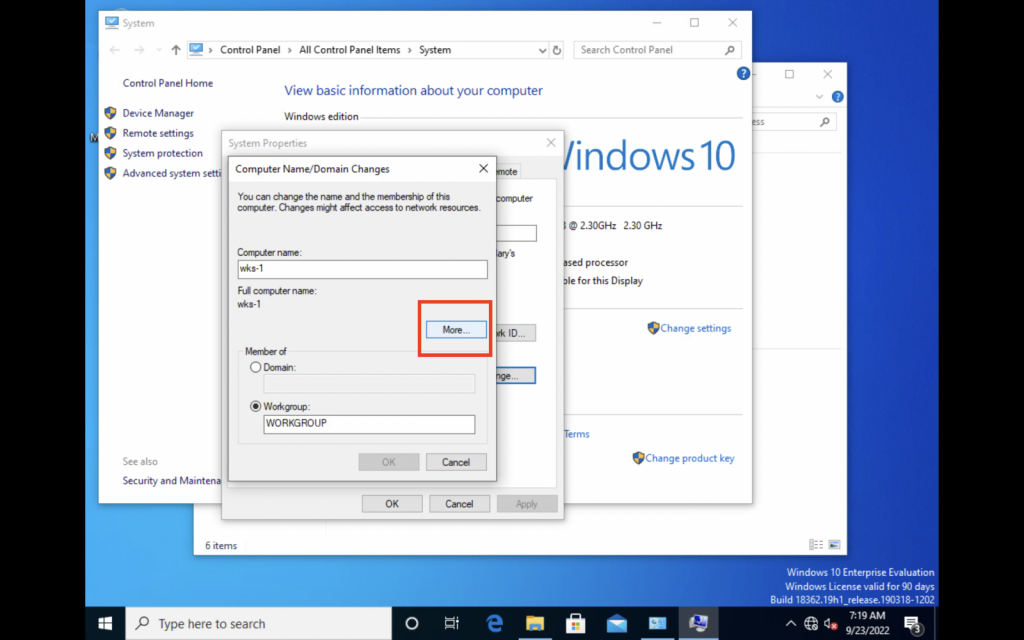
Client configuration
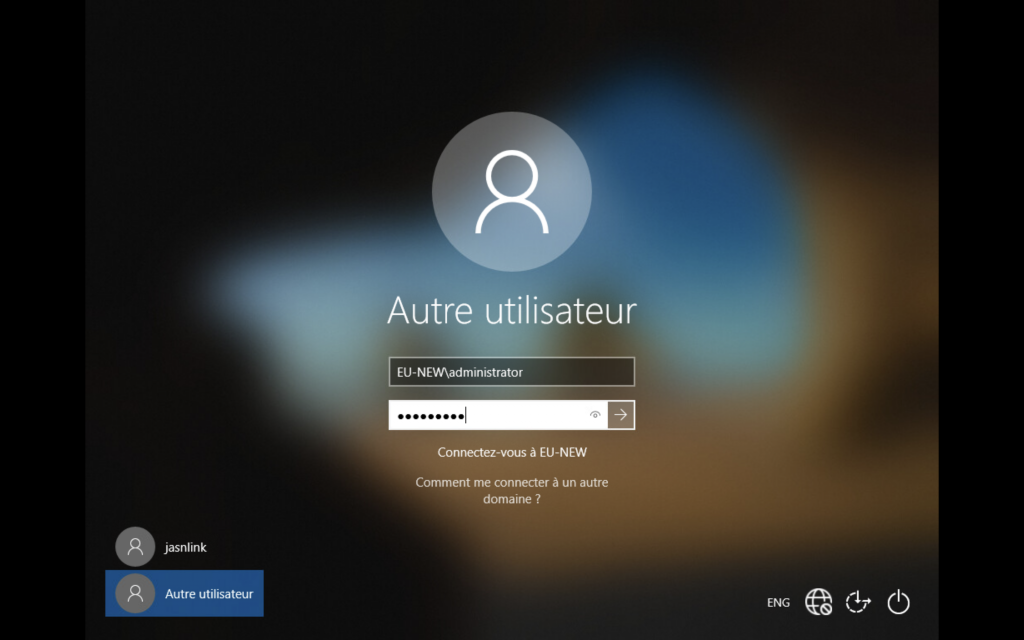
Our server is now ready to authenticate clients as soon as they join the same domain eu-new.lan. We must first configure our client to be part of the same network.
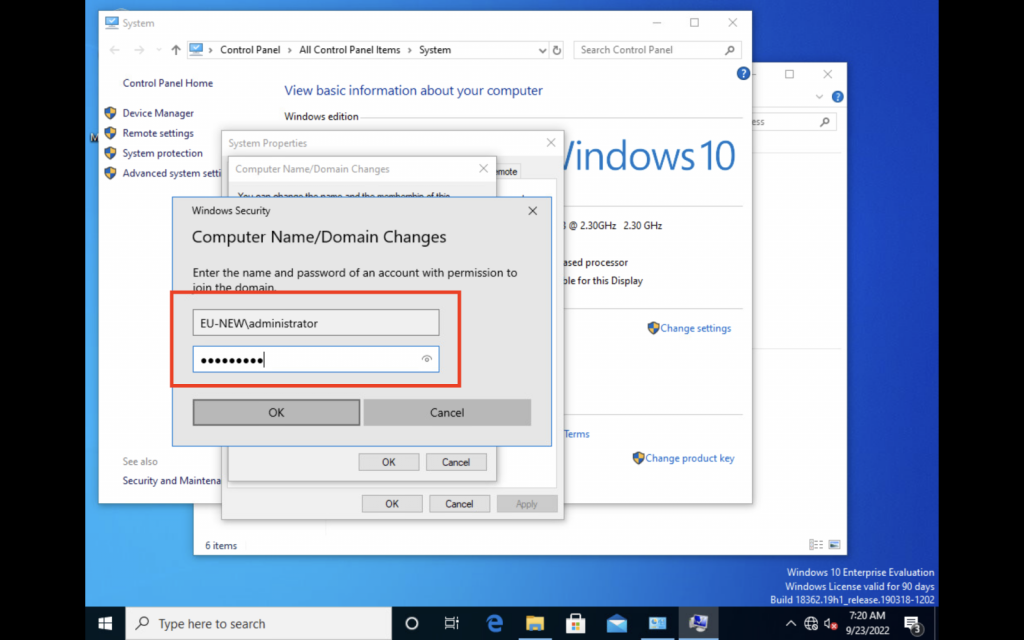
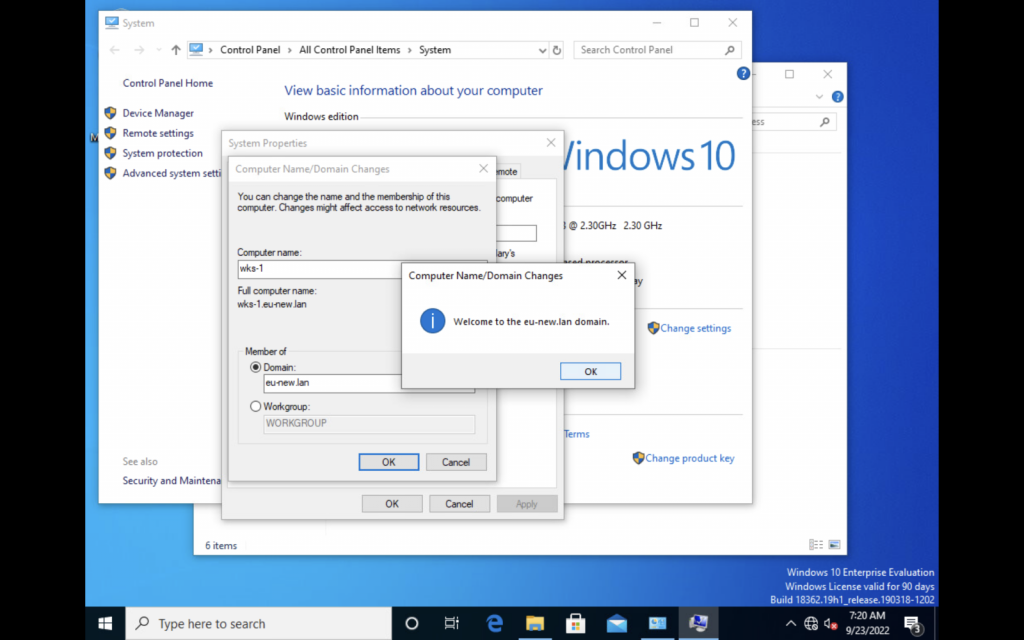
Congratulations, the client wks-1 is now part of the domain eu-new.lan and will now connect to our Primary Domain Controller in order to authenticate and login.
Now if your organization has 10 or 100 client computers, they can all be shared with the user account.
Conclusion
In this guide, we have learned how to configure our Windows Server 2019 and install Active Directory. This allows to manage user accounts and authentication through a centralized server called the Primary Domain Controller.
After that, we configured and connected our client to the domain is now being managed by the server. All of the company's machines can now be managed this way and an employee can simply login to any of them with his user account.
This is only the beginning of what Active Directory can do. Our next step would be to read our guide on how to configure the DNS server and integrate it into Active Directory on our Domain Controller and eventually administer rules to the whole company via Group Policy Management.